Public Safety, Police and Security Professionals Can Help Assess Campus Security Threats
One strategy is to assess the threat posed by a potentially dangerous individual. Doing that may require a mix of counselors, staff, and public safety, police and security professionals. "The key component: being proactive and identifying if he or she presents a real threat," says Sean Ahrens, practice leader in security consulting and design services with Aon Risk Solutions.
Kennesaw State has assembled a behavioral response team, Lang says. Its mission is "to provide a proactive, planned, and coordinated approach to the identification, prevention, assessment, management, and reduction of interpersonal and behavioral threats to the safety and well being of the Kennesaw State University community."
To help in these efforts, the university also has implemented a "red flag reporting" system accessible via the school's website, through which students and staff can report behavior that warrants concern. Examples include threatening online postings and writings that communicate dangerous intentions to oneself or others.
Of course, it's not possible to remove every danger. Still, "the more people involved, the better the chance to mitigate risks," says Jon Evenson, director of emergency management services with The RJA Group.
Even as school faculty and staff take steps to evaluate an individual, they need to comply with the privacy requirements under various regulations, such as the Family Educational Rights and Privacy Act (FERPA) and the Health Insurance Portability and Accountability Act (HIPAA). Both limit the amount of students' personal information that can be shared, Ahrens says.
Also key is clearly delineating the roles and responsibilities of everyone involved in planning for and managing any incidents that might occur. "You don't want five different groups thinking they're responsible for decisions," says Evenson.
The Communication Plan
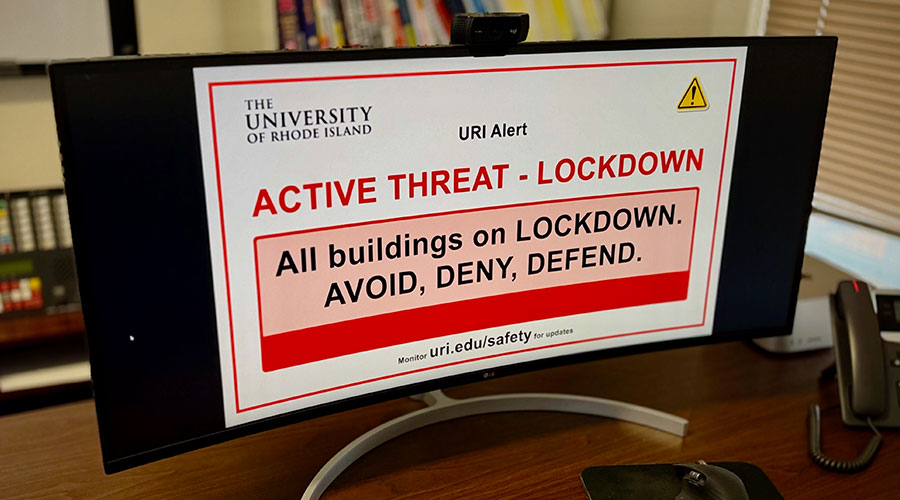
Determining ahead of time the way in which communication will flow in the event of an emergency is critical. Accurate, timely communication before and during a safety event can help everyone involved better manage the impact, Ahrens says.
The communication plan should identify the roles different individuals will play in disseminating information, as well as the technical systems that will be used. For instance, students should know how the administration will reach them during an emergency, Ahrens says. Will they be sent text messages or email? Or both?
Communication should continue throughout an event, Ahrens adds. "If you don't update the information, people will draw their own conclusions — possibly incorrect ones," he says. For instance, individuals often want to leave whatever building they're in, thinking it's safe. However, that could put them right in the path of a dangerous individual. "The excitement and overall anxiety of the event take over," Ahrens says.
Although it's not as critical as ensuring accurate communication with the individuals directly affected by the event, facility managers should also keep tabs on any communication to the outside world occurring via both traditional and social media, Evenson says. Otherwise, the university may have to respond to inaccurate stories about an event that are being spread via Twitter or Facebook.
What Threats Pose the Biggest Risk?
An important early step in preparing a crisis response plan is to develop a list of possible events that could hit the campus, such as natural disasters, burglaries and violent attacks, says Gary Margolis, managing partner with Margolis Healy & Associates. Of course, the total often can top several dozen. No school has the resources to prevent every potential threat, so it's important to focus on those that are most likely to occur or inflict significant harm.
Margolis advises looking at potential security and safety events from the perspectives of vulnerability, impact and probability. For instance, how vulnerable is the campus to a tornado? Can its vulnerability be reduced by fortifying the buildings on campus?
The next step is to look at the possible impact of each threat. Clearly, tornados or school shootings typically have a greater impact than, say, a stolen laptop. On the other hand, the probability that a laptop will be stolen during any school year exceeds the likelihood that a more serious incident will occur.
The idea is to complete this analysis for the entire list of potential threats, ranking each and developing plans for events that hit certain thresholds. "The point is to pick the events based on discussion and reflection, not arbitrarily," Margolis says. "Build reasonable strategies to address the range of incidents that colleges can face."
— Karen Kroll
|
Related Topics: