Cost-Effective Path to Better Security
Security layering can help conquer threats by dividing up a building into rings of increasing protection
In the aftermath of Sept. 11, new buildings and their environs will be designed using security criteria that would have been unthinkable in the recent past because of cost constraints and other design considerations. What’s more, existing buildings will be modified and retrofitted where practical to improve security. The increase in security will require a change in design mindsets to minimize the construction, operating and maintenance costs of security measures. Many tools and potential solutions are available. One of the most useful of these tools is an approach called security layering.
At its most basic, security layering refers to concentric rings of site and building security. These rings typically progress from the exterior boundaries of a site to the exterior building shell to increasingly secure areas within the building. The rings are not always symmetric or well defined, but each one represents an increase in security hardening against external threats as one moves inward from the site boundary or building exterior.
In a layering approach, design consideration must be given to the flow of people and material as they move though public, private and restricted building areas. Controlled paths need to be established in conjunction with each layer of security. This is where design with security concerns in mind can minimize implementation and future operating costs.
Equally important are the internal security layering requirements that segregate building spaces from one another — a key requirement when multiple tenants or departments with differing security needs occupy a single building.
Securing Core Areas
Most buildings share core areas that include vertical transportation, electrical and telephone rooms, janitor closets, and public amenities like parking areas, lobbies and toilet facilities. A successful security design must not only plan for the flow of people and material during occupied and unoccupied hours, but also consider how this flow affects the sharing of public and service areas.
For example, building access from surface or underground parking facilities needs to be segregated and directed to a common access control point to minimize security staffing and other operating costs. Because of past incidents in high-profile buildings, underground parking may in the future be limited or not be provided at all.
When designing security to maintain segregation of building areas, life safety code requirements must be observed, and the required emergency egress paths must be maintained using appropriate egress hardware. Though it sounds simple, this is one of the most difficult requirements to implement because it requires comprehensive understanding and interpretation of building codes and close coordination of door hardware, security system and fire alarm system requirements.
Design Principles
Proper design and use of the built environment can assist in effective security layering. The following four design principles are key:
- Natural surveillance: The ability to keep potential threats easily observable in parking areas and building entrances.
- Territorial reinforcement: Defining private and public areas in the facility or campus using landscape plantings, pavement designs, gates and fences
- Natural access control: Design of streets, sidewalks and building entrances to indicate clearly the public access routes and to discourage pathways outside the secure areas, using structural elements to complement electronic access control.
- Target hardening: Design using features that prohibit entry or access, such as window, door and air intake location; locks; dead bolts; electronic card access; and closed circuit television (CCTV).
To enhance security, building exteriors will in the future likely be designed with fewer windows and other openings; exterior windows and doors at the lower floors will be reinforced. Fresh air intakes will no longer be at grade. The number of outside entrances for pedestrians on foot or from parking areas will be reduced to channel the flow to lobby security stations that can be staffed with the minimum number of personnel.
Underground parking, loading docks and service entrances will be located and designed to segregate and effectively control the flow of personnel and goods using transition areas. Building service areas, toilet facilities, corridors, and electrical and telecommunication closets will be located so that the building’s net usable space can be subdivided, segregated and secured as needed to meet the requirements for each tenant or department’s security, while maintaining the code-required means of egress.
Technology’s Role
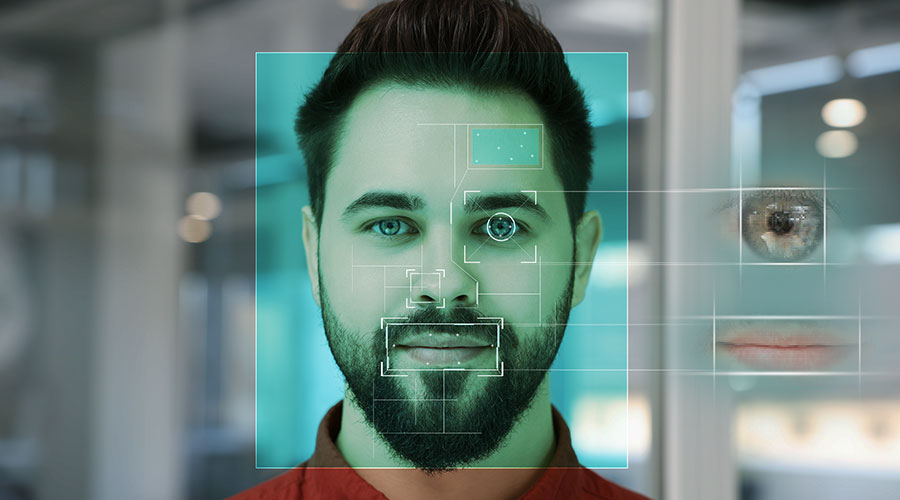
In addition to physical barriers, a layered approach to security typically requires electronic security systems — different combinations of things like badges, biometrics, card access, door alarms, CCTV and package scanning machines in different combinations — along with personnel trained to make the final decisions. The effective placement of these systems can reduce staffing requirements.
The upper box on page 53 shows the placement of card access devices and personnel to control access to building core areas from the outside while minimizing staff needed to handle visitors.
In the example shown, everyone who wants access to non-public areas of the building is directed to the turnstiles that control access to the elevators. Visitors can gain access when authorized by the security personnel.
In a building similar to the one in the example, delivery trucks could gain access to the loading dock after being cleared by the security staff. Depending on the security level required, access to the freight elevators can be further controlled after inspection of the cargo.
Further security layering can be implemented for personnel and material that have been cleared for access to tenant spaces. The bottom box on page 53 shows a typical arrangement of multiple-tenant floors. Tenant security is maintained with the use of card readers to control access into the space. Tenants that need to track personnel who enter and leave their spaces can use their own card readers. Tenant personnel can gain access to the toilet facilities while maintaining security; the use of keys or card readers at the toilet facilities is an option that needs to be evaluated separately. Those making deliveries from the freight elevator need to request access to tenant spaces via telephone or intercom.
CCTV systems with motion detection can provide continuous monitoring that is useful not only to grant access to the protected spaces, but also to provide forensic evidence needed to investigate security-related incidents. Digital CCTV provides for easy retrieval of information on demand without the time-consuming searching required by older analog systems.
Although security layering is a valuable strategy for controlling the flow of people and materials within the building, it isn’t the whole story. Operational plans are needed to limit access only to suppliers and staff with legitimate need. Deliveries of supplies from known sources should be coordinated in advance. Delivery times may have to be restricted to off-peak hours to avoid unnecessary delays to building occupants. For particularly sensitive areas, requirements for background investigations of outside contractor staff may need to be established to prevent “Trojan horses,” such as bugging devices, from being introduced into the building during construction, maintenance or deliveries. Emergency plans need to be developed and tested with the building occupants to address different types of security-related emergencies. Exit and emergency pathways need to be established for different scenarios.
Special measures and additional staffing may be required for special events, such as social functions and tenant relocations, where a large number of strangers may require access to secured areas.
In new buildings, security layering can be integrated into the original design in a very cost-effective manner. But, of course, occupants of existing buildings are demanding increased security as well. In most of these buildings, security improvements are more costly to provide because of significant additional staffing costs or building modification costs to redirect the flow of people and materials. Many existing buildings were designed with multiple entrance pathways; these buildings must add significant security staff or make costly changes to the building itself to provide minimum levels of security. Building owners will have to treat those additional expenses as a cost of doing business; tenants are demanding increased security, and those measures carry additional costs. Another challenge for existing buildings is that the security layering approach requires both building owners and tenants to accept changes in behavior without developing a trench mentality.
When it comes to upgrading security from what was acceptable in the past, there is no free lunch. To put it another way, no pain, no gain.
With new buildings, costs can be minimized. Doing that requires building owners to remember two key points: first, that during the design process it is never too early to plan for security; second, that many tools are available to provide security. And it’s not just building owners who need to think in a new way about security in new buildings. The increased demand for security also will require a change in the mindset of architects and engineers. Design professionals will have to consider how to incorporate into building designs the sometimes conflicting desires and requirements of building owners, occupants, vendors, visitors and governing agencies.
If everyone on the design and construction team focuses on security early and consistently, security does not need to be expensive and in many cases can be incorporated with minimal impact on the tenants who spend a great deal of their everyday lives in the building.
It’s also important to remember that effective security requires the building owner to address both operational and security technology issues as well as architectural factors. For example, it is critical that the issues of security staffing and training be addressed. With solid planning and an awareness of the tools available to designers, building owners can achieve the security levels they need without high ongoing costs.
Jeffrey Cosiol is a principal and project director at Kling Lindquist, a 500-person architecture, engineering and interior design firm headquartered in Philadelphia. Among other areas, Cosiol oversees the design and implementation of computer-based security systems and has significant expertise in government procurement matters regarding security projects.
For Airports, New Security Measures Pose Tough Questions
Tightened security at the nation’s airports is putting a squeeze on more than just travelers once accustomed to showing up at airports just minutes before their scheduled flights.
It has airport operators in a pinch, too.
Security changes ordered by the newly created Transportation Security Administration (TSA) will require structural changes in airports to accommodate new security screening devices and space for additional security checkpoints.
By year’s end, airports will be required to have systems in place that allow security workers to screen every checked bag for explosives, have a bag-match program that ensures that no checked bag is placed on an aircraft unless the passenger is aboard the aircraft, and provide passenger and baggage reconciliation with every bag that fails explosive detection screening.
While there’s debate among airport operators over how they will do that, it’s clear how the federal government would like it to be done. TSA favors the installation of systems known as Explosive Detection Systems (EDS). And while the government says it will foot the bill for the purchase of the million-dollar machines, airports will be required to reconfigure spaces to make room for the devices, which can measure up to 8 feet wide by 16 feet long and weigh as much as 8 tons.
What some airports are hoping, says Marion White, a vice president for HOK Aviation, an international architectural firm, is that TSA will allow handheld security devices to be used until newer and faster EDS devices are approved for use. Those newer systems measure almost half the size and weigh two-thirds less than systems in place now.
Assuming that airports will eventually implement the larger equipment, operators did get some relief recently when TSA approved methods of screening bags without having passengers present. That means those machines can be taken out of ticket and baggage check areas, where they have been located since the start of this year, and placed inline with baggage operations located behind ticket counters, or in the baggage handling area. That frees up space in ticket lobbies where long lines of passengers would form waiting to have their baggage screened.
On the other hand, if a bag fails screening, airports will still be obligated to have the passenger present to open the bag. That move will require installation of technology to match passengers with bags through the use of boarding passes or other means. And airports will still have to accommodate the machines in baggage operation areas, even if it means adding on to structures or building new spaces.
“Some existing airports literally don’t have the space in the building,” White says.
In existing facilities, TSA will fund the costs of reconfiguring space. New facilities, however, are going to have to incorporate the additional space required into designs.
TSA’s assumption of airport security also is requiring airports to accommodate new security screening areas for airport and airline staff. No longer will photo identification badges be sufficient for airline workers to gain access to gate areas, either inside the airport or on the ground.
The addition of TSA security staff to airports is likely to necessitate airport additions. As federal employees, security workers are given access to the same facilities as air traffic controllers and immigration officers. That means the addition or expansion of locker rooms and workout facilities, says Paul Bollinger, vice president of aviation client services for HDR Architects.
“The airport operator is in a tough position,” Bollinger says. “I think across the country they’re doing a good job of handling the changes, but right now there are no answers to the questions they’re asking.”
— Mike Lobash, executive editor
Layering in Context
Security layering is one tool — albeit an important one — for effective security design. But it is still crucial to pay careful attention to the basics: defining the perceived threats; evaluating consequences if these threats are realized; and determining the likelihood that each threat will be realized.
Neighborhood environment, vagrants, vandalism, theft, disgruntled employees, and terrorism are among the issues to consider. What’s more, the information age has created a new set of security problems in safeguarding the physical sites and equipment where critical information resides. Disruption of utilities can be devastating. The locations of central utilities and services need to be evaluated and protected as required by the use of the building.
Nor does layering change the principle that security needs to be site- and building-specific. Urban and suburban buildings are subject to different threats and risks, so they have different security needs. Once these are established, appropriate measures can be taken to reduce the likelihood or consequences of each threat, and the different spaces can be located within the building to minimize risks and operating costs. It is in matters like these that security layering can be valuable.
The U.S. Department of Justice’s Vulnerability Assessment Guidelines can serve as a valuable reference for the protection of buildings in accordance with their types and uses; some layering issues are addressed.
Security Challenges and Priorities at the Federal Reserve Bank
To say that facility executives have their work cut out for them with security is an understatement. But consider the challenges of securing an 80-year-old building in the middle of a downtown business district — and a Federal Reserve Bank at that.
“The biggest challenge is providing physical security for a building not designed with the security risks we face today in mind,” says Jack Vandermade, vice president of the Kansas City, Mo., facility.
The physical limitations of the facility are obvious — and daunting. There is a limited vehicle stand-off area: The building and the street are separated only by the width of the sidewalk. There are too many entrances, and they weren’t placed with screening in mind. And the receiving dock is immediately adjacent to the main facility.
To determine what measures were needed to address those physical weaknesses, Vandermade had to identify the most likely risks. “Is your risk stand-off distances?” asks Vandermade. “Is it explosives carried in a backpack?
Screening vestibules outside the perimeter, before people entered the building, were needed. A hardline to prevent vehicles from running into the facility was also necessary, as was a remote inspection station for delivery vehicles.
Once the priorities were identified, the next hurdle was getting support for funding. On that count, educating employees about the need for improved security was critical.
Another issue was the security staff. Concerns about unqualified security personnel have become an industry-wide issue. Attracting and retaining qualified personnel remains critical for the Federal Reserve.
Now, almost eight months after Sept. 11, sustaining support for security is an ongoing challenge. “The urgency for security is not as strong as it was Sept. 12,” says Vandermade.
— Angela Maas, managing editor
Related Topics: