Security Building Blocks
With as many security threats as there are ways to mitigate them, facility executives look for best practices to form the cornerstones of successful security plans
By Greg Zimmerman, Executive Editor
When planning building security, facility executives have to consider threats that range from break-ins to bombs to biological agents. Given the strides in security technology, the nearly constant threat of terrorism, as evidenced by the recent bombings in London, and the increased blurring of the lines between facilities, IT and security, facility executives have more to think about than ever as they work to protect their organizations’ people and property. The challenge is combining all these considerations with existing security protocol to arrive at a total security plan that protects building occupants without being overly intrusive to day-to-day operations.
While the security situation at every building is different, many best practices are applicable to any type of building in most types of organizations. From integrating security technologies, such as access control and video, to standardizing systems across an entire portfolio, these best practices can help streamline a facility’s security operation.
Know what you need
When examining how to bolster a security plan with new technology or a new system, most experts say that proceeding without conducting a risk assessment is a mistake.
“The risk assessment is the most important thing you can do for a facility,” says Bill Mellin, portfolio manager for Gale Global Facility Services. “It allows you to put in a security system that best protects from threats you’re most worried about, whether that be terrorism or espionage or whatever else.”
The first step in a facility risk assessment is identifying the nature and operations of the building. “We do that from a loss perspective,” says John Shriner, senior vice president and director of physical security for Wells Fargo. “We ask ‘What are the business impacts if this facility were to go away?’ Then we develop the appropriate safeguards based on the things that could cause that to happen.”
For Shriner, the risk assessment process includes incorporating data obtained from the Department of Homeland Security and other sources on known or suspected threats. “The information we glean from government agencies is very important to our assessment process,” he says.
Working with local agencies and police is also a key step. “We work very closely with law enforcement,” says Jim Weslager, vice president of corporate security for PNC Financial Services Group. “We’ve got a number of field officers of the FBI with whom we meet on a monthly basis. We talk to special agents regarding crime trends.” Weslager says they spend time talking about national security concerns, too.
Shriner’s risk assessment, or risk modeling as he calls it, involves assigning each building a score. That score drives the selection of security applications used in the building — whether the building requires access control, video, intrusion alarms or other equipment. A similar system of prioritization is in place for the buildings at Georgia Institute of Technology. Bob Lang, Georgia Tech’s director of homeland security, says that his buildings are rated based on major, moderate and lesser risks, depending on the building’s operation and whether the building stores potentially dangerous items.
“A major-risk building would include anything that houses chemicals or gases that would be immediately hazardous to health,” he says. “For instance, phosgene — an agent potentially used in biological terrorism — is used in a lot of experiments and activities that support high level research. We have to control who goes into those buildings, and there are procedures in place for who has access.”
A Job Never Done
Of course, risk assessment is never complete — it’s an ongoing, sometimes reactive task. After the terrorist attacks of Sept. 11, 2001, many facility executives revisited their security plans and implemented new procedures and technologies. Responding to an escalated threat level — as indicated by the national color coded system — became a key consideration for many facility executives. But beyond the threat of World Trade Center-like tragedies, the post-9/11 culture of heightened alert for terror threats got facility executives thinking more about their security situations as a whole.
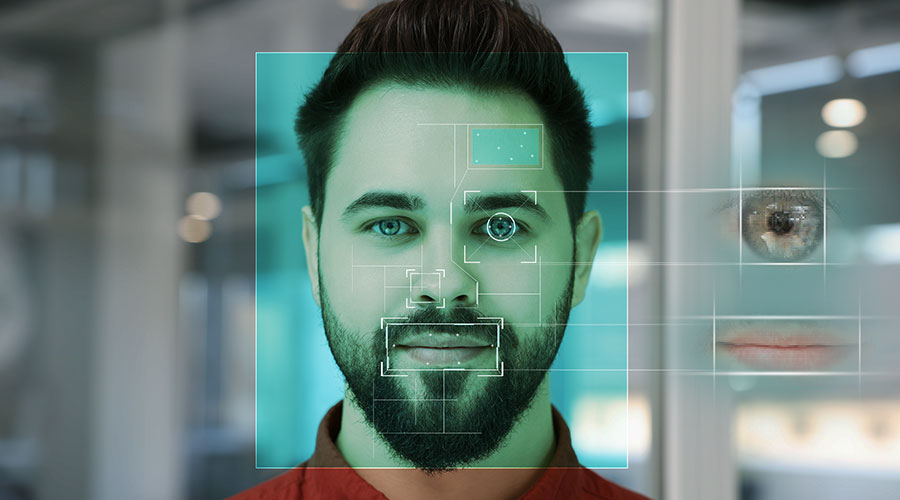
“The single biggest change since 9/11 is more frequent use of positive identification for building occupants,” says Mellin, “This is true in any building, not just critical ones like data centers.”
Responding to the escalating color-coded threat level system with increased control of access to buildings is an example of an across-the-board security best practice, regardless of building or organization type. In most cases, this involves moving the security perimeter of a building out to an alternate, more secure point, whether that perimeter is a guard desk, the actual front door or blast protection barriers on the street.
At Georgia Tech, if the threat level rises from yellow (elevated) to orange (high), Lang says that in buildings deemed major risks, only people with card access will be admitted immediately through the front door. Other visitors will need to signal a guard who will check the person outside. If approved, the person is given access and can sign in at the door, rather than at a guard desk on the inside of the building. At PNC, if a building has three or four entrances, all but the main entrance is closed so everyone who enters the building has to pass the security station. Additional guards are also deployed throughout the enterprise, says Weslager.
In addition to people, packages coming into PNC facilities are scrutinized as well. “If we go to orange, we inspect all delivery vehicles,” he says. “We validate expected deliveries and balance that against the day’s manifest before we let them into the facility.”
AT&T employs a similar strategy. “At the time the level is raised, all shipments to the loading docks will be checked and all credentials will be verified prior to the shipment being made,” says Vinnie Placco, security real estate manager.
Using Technology
Technology updates have allowed for more flexibility in the way systems are deployed, both separately and in conjunction with one another.
Access control is one area where facility executives have opportunities to get high tech. “Card access has the biggest capability for integration,” says Wells Fargo’s Shriner.
At PNC, the same access control system is used company-wide, which is convenient for employees who often travel from one facility to another. It’s also convenient for security purposes.
“If we have to terminate an employee, we’re able to immediately deactivate their access card,” says Weslager. “We can electronically shut them off at the flip of a switch throughout the enterprise.”
Even with the convenience enterprise-wide access control provides, it’s important to design the system so it can remain flexible. “Installing hardware or software of a proprietary nature should be avoided so that true global integration is possible,” says Brian McLeod, global real estate security associate at AT&T. “Avoid a fragmented approach to enterprise access control.”
Avoiding the fragmented approach also means looking at access control systems as a vehicle for integration with other devices. Access control and video are increasingly being linked to relieve some of the burden of around-the-clock live monitoring. This is a strategy being employed in a variety of security situations, from the corporate world to institutions like Georgia Tech.
“If someone uses a card at a particular door, the camera automatically goes to that door and records the activity,” says Lang. “Now we know a face with a badge.” If there’s a security problem, Lang can check the access control system’s log and compare it with the face recorded on the camera to see if the two match. If they don’t match, it means someone’s access control card has been lost or stolen, but Lang can still go to the authorities with the footage from the camera.
As a security strategy, video cameras are used so commonly that most people don’t even notice them anymore. In fact, the average American is picked up by a camera about seven times per day, says Lauris Freidenfelds, vice president at Sako and Associates. Of course, video is still a key component to facility security plans in all types of settings. And updates to technology have brought efficiency to how video is used, recorded and reviewed.
For financial institutions, video is probably the most critical component of the security plan. Making that video accessible quickly and easily has allowed PNC to stay ahead of the security curve. In addition to monitoring the access control system, Weslager can monitor video on the corporate network as well.
“We have a little over 500 digital video recorders (DVR) employed enterprise-wide,” says Weslager. “I can sit in my office or be on my laptop on vacation and see all the video in all the branches and all major buildings. So in addition to allowing us to shorten the time for investigation, we can be proactive.
“If we’ve got a bank robbery, within a minute, we are notified by dispatch. Within 60 seconds, our staff is pulling video of the robbery from the DVR. When the police show up, we’re ready to e-mail them the physical descriptions and photographs of the suspects.”
Weslager also has video cameras covering fresh air building intakes, emergency generators and utility connections. By creating a video frame with a simple intelligent video algorithm, a DVR will automatically begin recording and an alarm will be sounded if the frame is broken by movement.
Virtually There
The “virtual command center,” which Weslager uses to respond to robberies, is also employed at Georgia Tech.
“What we have done is changed from a hardened command center to a virtual one,” says Lang. “We are doing that based on our wireless network so that we don’t all have to be in one room.”
The system uses voice-over-IP so that traditional phones or even data banks aren’t necessary — which saves a lot of money. If there is a campus-wide emergency, each of the five area managers — Lang has divided the campus into five security zones — can log onto the system to coordinate what should be done next.
“Originally, all 150 building managers would be communicating directly with the command post,” says Lang. “You can’t have that many people talking at once.” So Lang designated the area managers and created the virtual command center so that if there is a problem at any individual building, or campus-wide, building managers can communicate with the area manager, who in turn communicates with the command post. The hierarchical structure ensures that the virtual command center isn’t flooded with too much chatter at one time.
Eye on Occupants
Whether working in cyberspace or at a facility itself, most experts say that one of the most important aspects of any security plan is gaining the cooperation of occupants. This means educating occupants on how elements of a facility’s security plan are protecting them and also creating a culture where security is always a priority in the minds of occupants. The goal is for occupants to not only look out for themselves but also keep a wary eye on others, both in terms of suspicious behavior and any fellow occupants who aren’t following existing security protocol.
Weslager says that at PNC’s operations facilities and data centers, both occupants and visitors are required to wear identification above the level of the waist at all times. If management at a facility isn’t enforcing that policy, he says he hears about it from occupants sooner rather than later.
“People assume that increased security will be a burden,” says Weslager. “But we’re finding that if we don’t have the level of security that people expect, then they challenge us to do so. And once we have security measures in place, people expect that we maintain them.”
So as good as the technology or security plan is, it is only as good as the people who use and enforce it.
“All of these issues can’t be done unless you have people being aware of their surroundings,” says Lang. “There’s a lot that goes into a security package. You can’t just say ‘I’ve got this new system’ and expect it to be foolproof.”
Related Topics: